Email is (and has been) a prime method of communication for businesses of all sizes. With email comes a whole slew of issues that are essentially synonymous with the technology; spam, information overload, phishing, and information privacy. Even Texas small businesses that only do business locally are at risk of these issues. Personal email accounts are equally at risk. Employing proper precautions and practices whenever communicating via email is very important to prevent the risk of security compromises, monetary loss, and even legality issues.
Telesys Voice and Data Blog
It wasn’t too long ago when the idea of video conferencing was a very complicated one. The technology just wasn’t there to make it a major benefit for companies. As conferencing technology has been innovated upon, however, it now presents a laundry list of substantial benefits. Let’s take a look at some benefits you can see by moving to video-driven meetings.
Nowadays a lot of accounts give you the option to set up two-step authorization; and, most of the time you probably should. The security and privacy benefits that your business can gain are substantial. Today, we’ll describe how to enable what Microsoft calls two-step verification.
Augmented reality has been one of the most cited emerging technologies for the past few years. It was the technology that was supposed to fuel Google Glass, the failed attempt at creating a pair of revolutionary smart glasses. Since then, there hasn’t been much press about AR in the mainstream media and not much is known about major tech companies’ attempts to improve AR technology.
There quite a few reasons that it makes sense for a small-to-medium-sized business to lean on outsourced assets. Let’s go over a few of the biggest benefits that you could see from bringing on these kinds of services, from both a financial and operational stance.
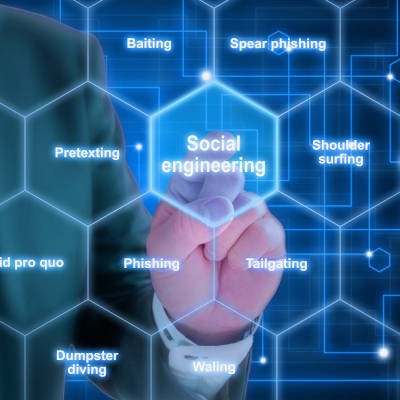
As prevalent as cybersecurity threats unfortunately are today, many users tend to overlook major threats that they just aren’t focused on nearly as much: social engineering attacks. Social engineering attacks are just another means for a cybercriminal to reach their desired ends, and therefore needed to be protected against.
Businesses require a lot of their Internet connections, especially if they’re using technologies like VoIP, screen-sharing, and/or webinar platforms. If you’re looking to incorporate these features, you need to be sure you have enough bandwidth to support them. We’re looking at a few reasons that your bandwidth matters, and how to tell if you have enough for your needs.
It can be a real head-scratcher when one of your otherwise well-performing employees routinely falls for the simulated phishing attacks that you roll out as a part of your cybersecurity awareness strategy. For all intents and purposes, the person is a great employee, but when it comes to acting with caution, they fail. If you’ve made a point to prioritize your staff’s working knowledge of phishing attacks, do you replace this employee? We’ll take a look at it today.
Microsoft 365 has been on the market for a while now, and we thought it would be a good time to go into the different tiers of the platform to give you an idea of what it is, why it is useful, and how your business fits into the latest cloud platform offered by Microsoft. Let’s start with what it is.
The cloud can bring numerous benefits to a business. Public cloud offerings can reduce technology costs, provide scalability and flexibility to a business’ computing infrastructure, promote collaboration, protect your business from data loss, and much, much more. What it cannot do, however, is guarantee the control some organizations wish to have over their technology infrastructure. Some businesses prioritize that control, while others are bound by industry and government-induced regulations. For those businesses, there is the hybrid cloud.
Social media - we can’t live with it, but we really can’t seem to live without it. People who frequently read our blog will notice how often we discuss Facebook, one of the biggest players in the social media space. Seeing as privacy is one of the biggest concerns today, we’re wrapping up our short series on Facebook by reviewing the settings you might not have realized were options on your Facebook profile.
Computers are great tools to get work done in the office, but only if they are used effectively. Employees looking to get more out of their Windows workstations can utilize the taskbar to get around faster. We’ll discuss some of the ways your business can take better advantage of the taskbar, as well as what it’s capable of.
As you company grows, you will need to invest a good deal of the revenue that you take in to keep operations from falling into complacency. In order to get a good idea what investments would be most advantageous, doing a proactive ROI analysis of project you plan to undertake can put your business in a position to be able to properly anticipate every aspect of a successful project. Let’s take a look at the variables of an ROI analysis.
Social media has completely changed the dynamics of how people communicate with one another. While some users might only keep in touch with friends through it, others--including businesses and brands--use it to promote their products. In an age where a picture can appear on thousands of devices all over the world, privacy has become a major concern for anyone using social media.
Windows 10 isn’t just a great operating system for getting things done--it’s also jam-packed with features that you might not even have known about. This week’s tip is all about some of the handy features that Windows 10 can provide for your office.
With more than $16 billion being scammed from more than 16 million people, there is clearly an issue at hand that could use some expert insight. Those who are familiar with Steven Spielberg’s Catch Me If You Can might know that the movie was based on the memoirs of Frank Abagnale, former con man and longtime security consultant of the FBI. With his 45 years of experience with the bureau, Abagnale can safely by considered an expert in cybersecurity and fraud protection.
For many tech-savvy individuals, the expression “Google it” is a well-tested, and approved, method to researching. Are you getting the most out of Google search? Today, we share useful tips on how to better optimize your Google search queries.
There is no denying that the cloud has exploded into the fastest growing business computing method, and for good reason. The cloud has a plethora of options that are designed to meet the needs of the modern business. Today, we examine how your business can leverage the inexhaustible supply of cloud options.
Business communications, which is the succinct way to say the sharing of information between people both internal and external to a company, is a key player in that company’s success. Here, we’ll analyze the different types of communication that a business could leverage, and the solutions that best enable them.
Any business in operation today needs to keep modern realities concerning cybersecurity at top-of-mind if they are going to successfully maintain the business going forward. One major issue to be cognizant of is the increasing prevalence of phishing attacks.
Mobile? Grab this Article!
Tag Cloud